After an Internet Service Provider installed your connection we usually just use it then there will come a time some kiddo in the neighborhood is now connected on your internet connection, and or you just got someone snooping on your data getting essential private data every time you browse into your bank account. Or maybe some ad company tracking your activity and providing you ads that are annoying or maybe serving you malvertisement or ads with malware. Sounds scary right? Yes it is but you can defend yourself.

The very purpose of this blog is to provide you on what you can do on your home network to protect you and other users connected to it, that way you can add a layer of protection even if you messed up while browsing and doing some bank transaction within the confines of your home. We have to remember sometimes common sense fails us so we need to get protected.
Lets start with the recommendations:
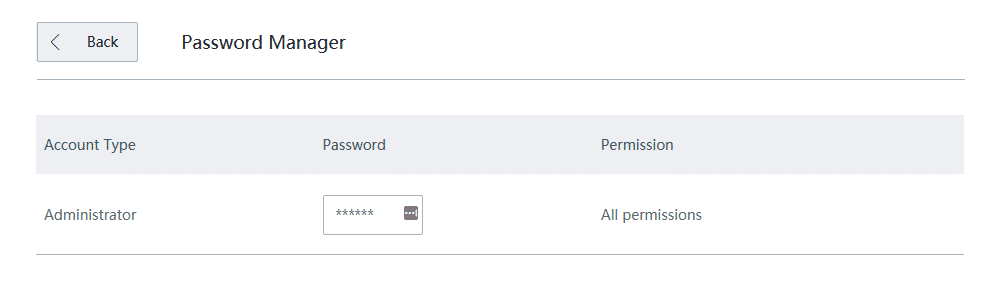
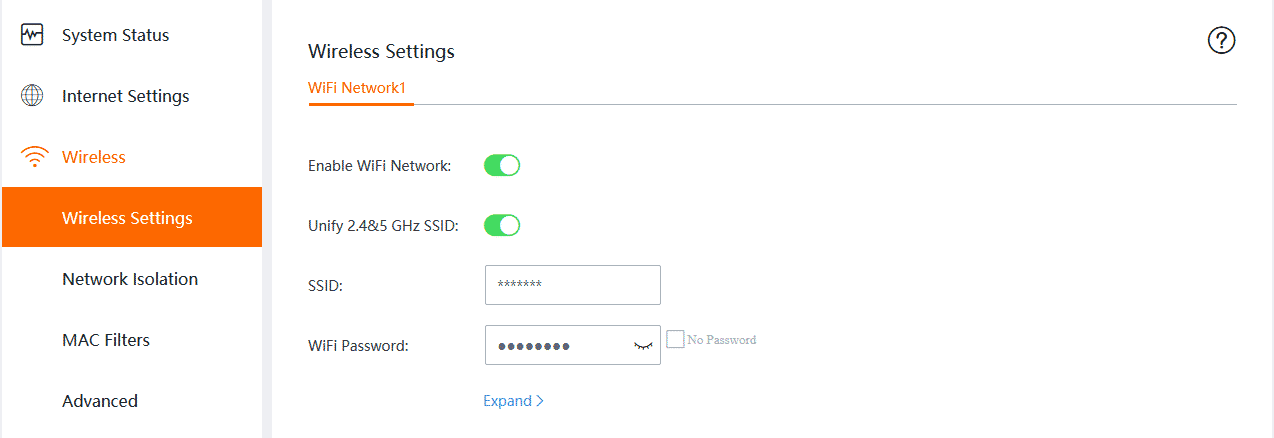
- Once you receive your modem / router from the provider the first thing you need to do is change 2 passwords, the password of the router and wifi for two reasons, first admin passwords are leaked around the internet, second your wifi password because it is usually not that strong enough and definitely it is using manufacture default which can be found again around the internet.
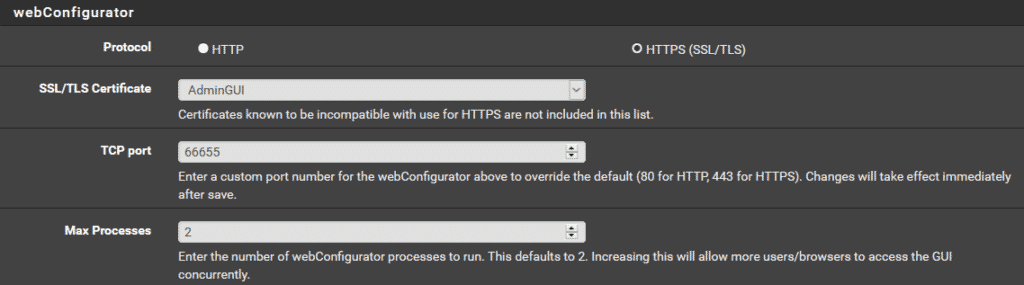
- If you can spare a bit of some moolah you can get another router where everyone can connect into and have more control to it like bandwidth and blocking access to the Admin GUI of the main router / modem provided by your ISP. But for this to be successful, you need to totally turnoff the wifi on your main router / modem then disable remote access to the Admin GUI, and to be sure make the access TLS/HTTPS then change the port that is only known to you. But some brands it just let you disable access to the Admin GUI via blocking access via WIFI.
- After setting up the ones above, you can now implement a firewall appliance and a network wide ad blocker and a recursive dns resolver. In our end we are using two components, a raspberry Pi for the PiHole with Unbound then a PFsense installed in a repurposed 1U Server.
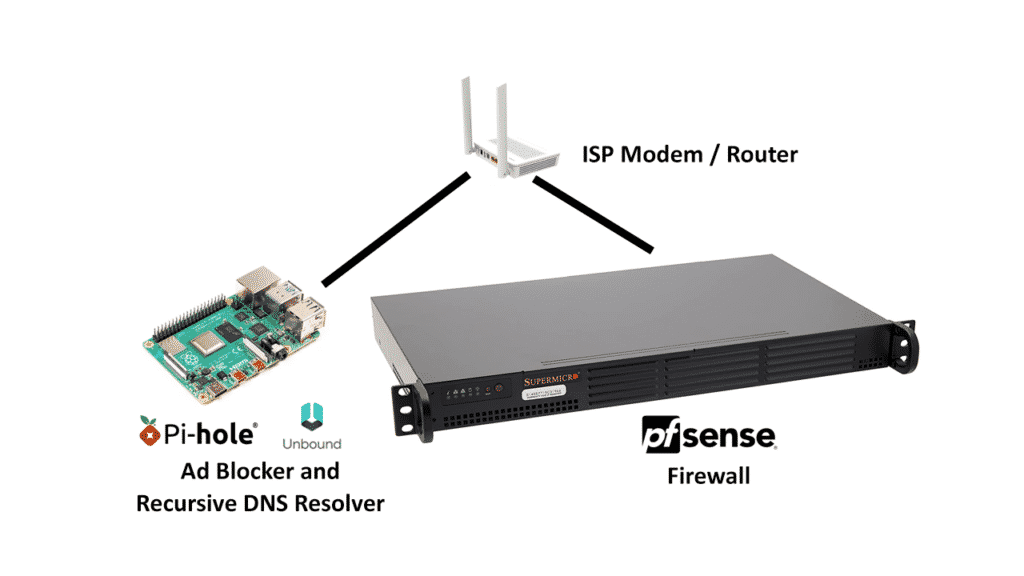
The setup enables us to block ads and resolve the DNS even before it reaches the firewall and we have better manageability when it comes to blocking external DNS Resolver such as 8.8.8.8 on the level of the firewall without affecting our PiHole and Unbound DNS resolver.
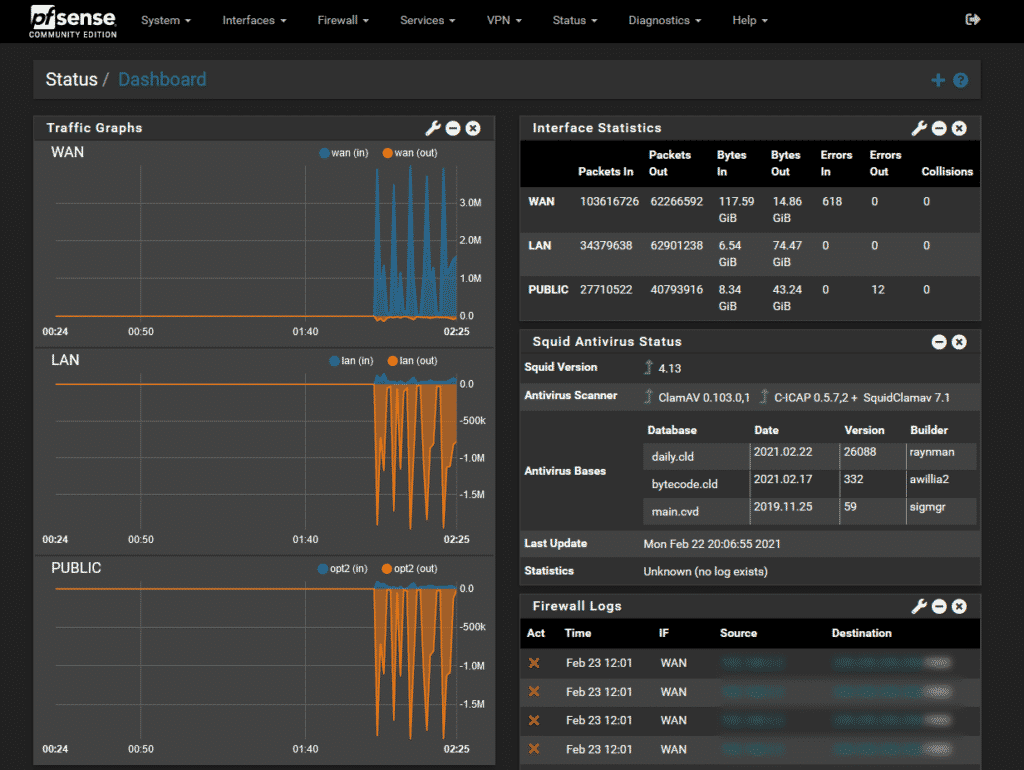
- On the level of your PFSense it will be important that you activate the following package which will be good enough to protect and monitor your network from intrusion, viruses and other attack vectors that may happen in your home network.
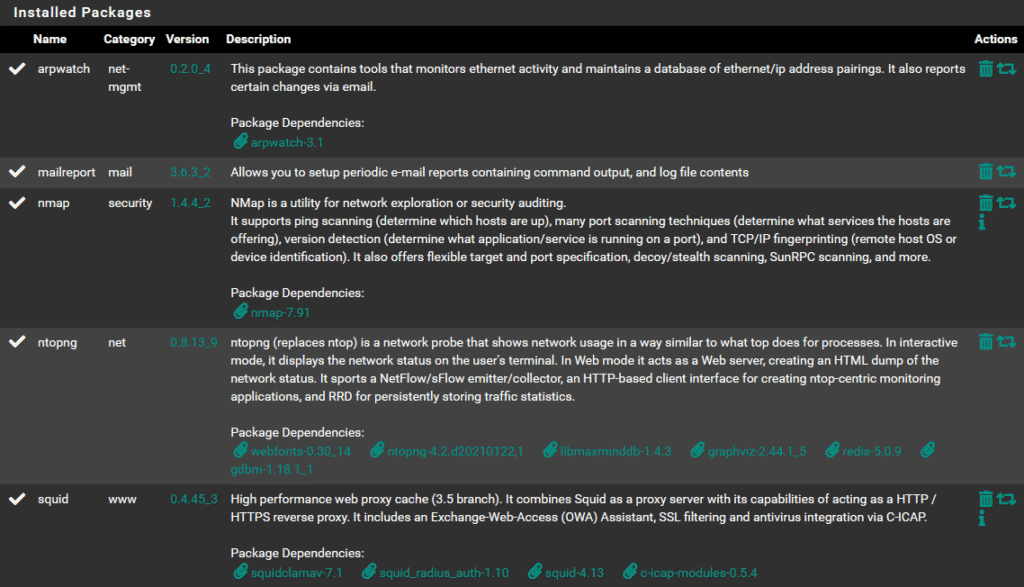
- ARPWatch – this helps me monitor ethernet activity and know the pairing and monitor errors for me to use for optimization and definitely check why some packets are blocked and rejected.
- Mail Report – a realtime report tool that I use to receive on my email for errors, intrusion, and other security and performance concern over the network.
- NMap – it helps me track and explore for the sole purpose of security audit when there is an attack over the network and effectively manage pass, block and reject configuration over my firewall rules
- NTOPNG – is a real time network monitoring dashboard where I can see flows and host and devices connected over the network and easily pinpoint violators and sources of probable vectors when we see it, it also help me monitor the total resource each user use and help me optimize the site and definitely security as well
- Squid Proxy with Antivirus – it is important to have a high performance web proxy cache in the network to improve site loading and a network wide antivirus and malware prevention and protection to stop possible vectors infecting devices in the network.
Extra Package that you can explore and use as well:
- Snort – snort help you track and block intrusion as seen and identified, this one help you stop a intrusion even before it reaches their target in your home network.
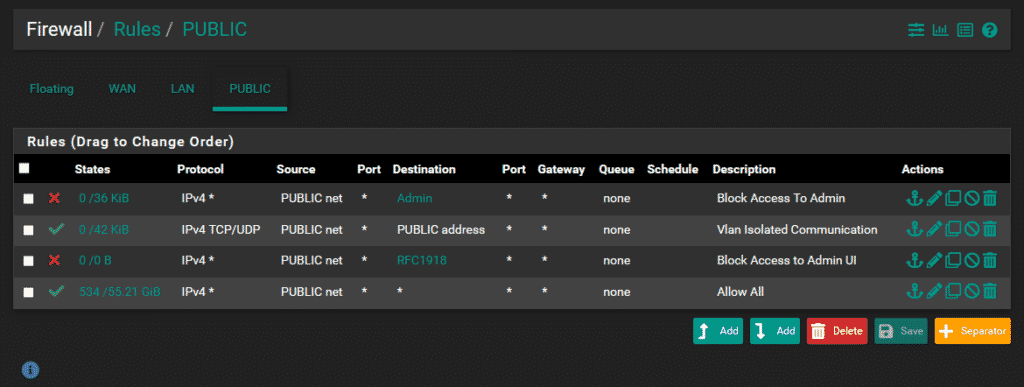
- And last it will be best to setup an IP isolation using Virtual Lan (VLan) where you can connect unsecured devices such as IP Cam, mobile phones and guest. You can setup an internet only VLan where your guest and other devices even if they are hacked the attacker can’t access your device GUIs, servers and other devices that needs to be secured. In our network this is our setup for Public VLan. On this part you can do this if you have a managed Switch to tag service ports.
It is important that you protect your infrastructure and at the same time protect each user within the network. Let me reiterate sometimes common sense fails and we as users fail to act fast when there is already an attack. It won’t hurt to add a layer of protection for the sanity of the whole home network.
A follow up blog will be released for each recommendations about how to set it up step by step.